The digital world has gifted us incredible conveniences, but it’s also unveiled new frontiers for deception. At the forefront of today’s evolving threats are AI-powered Deepfakes, once the stuff of sci-fi movies, now a very real cybersecurity nightmare for everyday internet users and small businesses alike. As a security professional, I’ve seen firsthand how quickly sophisticated digital threats can emerge. It’s my job to help you understand these risks, not to scare you, but to empower you with the knowledge and practical tools to fight back and take control of your digital security.
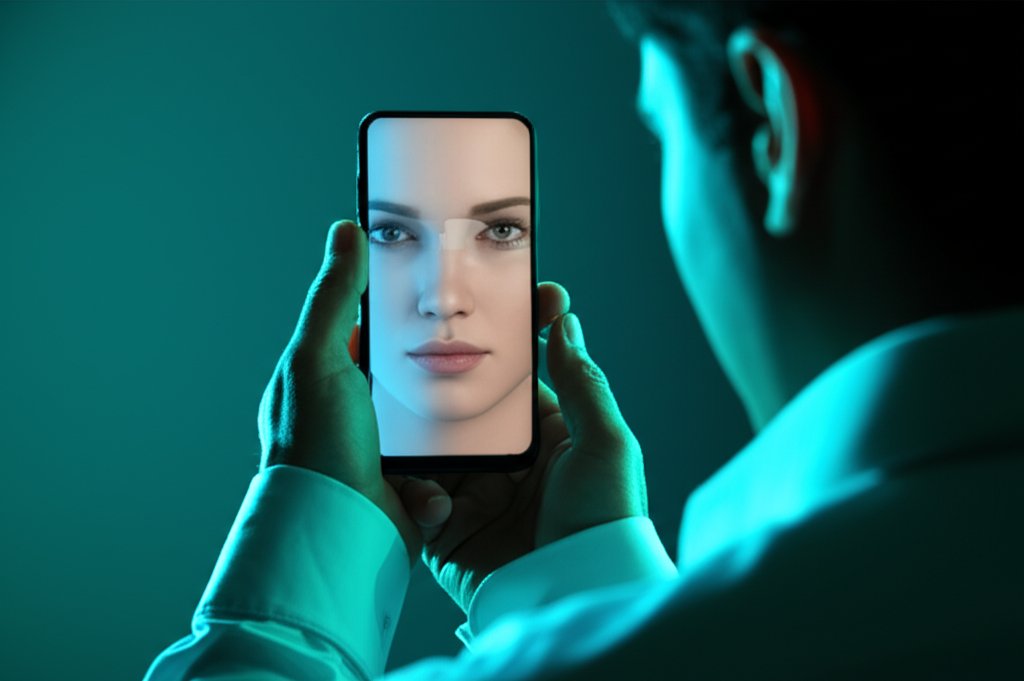
You might be wondering, what exactly are we up against? Imagine synthetic media—videos, audio recordings, or images—that realistically mimic a person’s voice, face, or mannerisms. That’s a deepfake. These aren’t just clever edits; they’re the product of advanced artificial intelligence, specifically deep learning and generative adversarial networks (GANs), which can create highly convincing fakes with astonishing ease. What makes them so dangerous right now is their increased accessibility, lower cost to produce, and rapidly improving realism. It’s a game-changer for cybercriminals, turning sophisticated deception into an everyday threat.
Let’s dive into how these digital imposters are being weaponized and, more importantly, how we can protect ourselves with robust, actionable strategies.
Privacy Threats in the Age of Deepfakes
In the digital age, privacy threats are constant, but deepfakes amplify them to an unprecedented level. They’re not just a nuisance; they’re a direct assault on trust and truth, capable of undermining personal reputations and business integrity. Deepfake scams are becoming alarmingly prevalent, especially for businesses, where the stakes are incredibly high.
Deepfake Scams Targeting Small Businesses
For small businesses, deepfakes present a terrifying new vector for financial fraud and reputational damage. We’re seeing increasingly sophisticated attacks where criminals use cloned voices or videos to impersonate CEOs, senior executives, or even trusted vendors. These impersonations are then used to trick employees into wiring money to fraudulent accounts, sharing sensitive company data, or granting unauthorized access. The human element, our inherent trust, becomes the most vulnerable link.
- Impersonation & Financial Fraud (The CEO Voice Scam): The headlines are full of these harrowing tales. Remember the UK energy firm that lost over $243,000 when a CEO’s voice was cloned and used to demand an urgent transfer? Or the Hong Kong finance worker who transferred $35 million after being tricked by deepfake video calls with a fabricated “CFO” and other employees, all seemingly legitimate? These aren’t isolated incidents. Attackers leverage these convincing fakes to bypass internal controls and exploit human trust, often targeting the very individuals with the authority to move significant funds.
- Business Email Compromise (BEC) & Phishing: Deepfakes make these age-old scams even more potent. Avoiding common email security mistakes is crucial here. An email asking for an urgent transfer becomes far more convincing when it’s followed by a “confirmation” call from your manager’s cloned voice, or a video call showing their face. The deepfake adds a layer of undeniable perceived authenticity.
- Reputational Damage: Fabricated videos or audio clips can be used to spread false narratives, damage a company’s public identity, or undermine leadership. Imagine a deepfake video of your CEO making controversial statements – the damage could be catastrophic before you can even issue a denial. This can erode customer trust and market value quickly.
- Identity Theft in Hiring: Scammers are even using deepfake identities in remote job interviews to gain employment and, subsequently, access to a company’s network and sensitive data. This is a stealthy infiltration method that bypasses traditional background checks and human perception.
Deepfake Dangers for Everyday Internet Users
It’s not just businesses at risk. Deepfakes pose significant dangers to our personal lives too:
- Personal Identity Theft & Fraud: Voice clones can be sophisticated enough to bypass voice-based bank security or trick family members into revealing personal information. A deepfake call from a loved one in distress demanding money can be incredibly persuasive.
- Blackmail & Extortion: Fabricated compromising content, often sexual in nature, can be used to blackmail individuals, causing immense emotional distress and financial loss.
- Misinformation & Disinformation:
Deepfakes are powerful tools for spreading fake news, manipulating public opinion, and creating social unrest, eroding the very fabric of truth we rely on. - Cyberbullying & Harassment: Non-consensual deepfake imagery can lead to severe emotional distress, reputational harm, and lasting psychological damage for victims.
It’s a serious landscape, isn’t it? But don’t despair. We have robust tools and actionable strategies to mitigate these risks. Let’s make sure our digital foundations are strong and our defenses are impenetrable.
Fortifying Your Defenses: Practical Tools to Fight Back
Protecting yourself and your business from deepfakes requires a multi-layered approach, combining fundamental cybersecurity practices with specific strategies for detection and response. Here are the practical tools and steps you can implement today:
1. Password Management Against Deepfake-Enhanced Attacks
While deepfakes directly manipulate media, strong cybersecurity fundamentals remain your first line of defense. And at the heart of those fundamentals is excellent password management. If an attacker gains access to your accounts—whether through a deepfake-enhanced phishing attempt or another method—they can gather data that aids in deepfake creation or exploits existing deepfakes. We’ve got to make it harder for them.
Actionable Steps:
- Use Strong, Unique Passwords: This is non-negotiable. That means no “password123” and no reusing the same password across multiple sites. Aim for complexity and randomness.
- Implement a Password Manager: Trying to remember dozens of complex, random passwords is impossible for anyone, which is why a reliable password manager (like LastPass, 1Password, or Bitwarden) is an absolute must-have. These tools securely store all your login credentials, generate strong new ones, and can even auto-fill them for you. It simplifies your digital life while dramatically boosting your security.
2. Two-Factor Authentication (2FA): Your Deepfake-Resistant Shield
Even with the best password, there’s always a risk of it being compromised. That’s where Multi-Factor Authentication (MFA), often called Two-Factor Authentication (2FA), steps in as your critical second layer of defense. It requires not just something you know (your password), but also something you have (like your phone) or something you are (your fingerprint).
Actionable Steps:
- Enable 2FA Everywhere: For deepfake protection, 2FA is absolutely crucial. Even if a deepfake-enhanced social engineering attack tricks you into revealing your password, the attacker still won’t be able to log in without that second factor.
- Prioritize Strong 2FA Methods: While voice clones might theoretically try to bypass voice-based MFA, standard 2FA methods like app-generated codes (e.g., Google Authenticator, Authy), physical security keys (e.g., YubiKey), or even SMS codes (though less secure than app-based) are significantly harder for AI to spoof.
- Critical Accounts First: Make sure you enable 2FA on every account that offers it—your email, banking, social media, and any business platforms. It’s often just a few clicks in your account settings, and it buys you immense peace of mind.
3. VPN Selection: Protecting Your Data, Hindering Deepfake Data Gathering
A Virtual Private Network (VPN) creates a secure, encrypted connection over a public network. While a VPN isn’t a direct deepfake countermeasure in the sense of detecting a fake video, it plays a vital role in your overall privacy strategy, which indirectly helps against deepfake threats. How so? By protecting your online activity and data from being easily intercepted or gathered by malicious actors.
Actionable Steps:
- Choose a Reputable VPN: Look for providers with a strict no-logs policy, strong encryption standards (like AES-256), and a wide selection of servers.
- Consider Key Features: Prioritize factors like speed, ease of use, and whether they offer features like a kill switch (which blocks all internet traffic if the VPN connection drops).
- Deny Them the Fuel: By encrypting your internet traffic, a VPN makes it much harder for cybercriminals to collect information about your online habits, your location, or even bits of data that could be used to build a profile for a deepfake attack. It’s about denying them the fuel they need to create convincing fakes.
4. Encrypted Communication: Keeping Deepfake Attempts at Bay
In an era where digital deception is rampant, knowing that your communications are secure is paramount. Encrypted communication tools ensure that only the intended recipient can read your messages or hear your calls, making them an essential part of your defense against deepfakes.
Actionable Steps:
- Use End-to-End Encrypted Platforms: For sensitive conversations—whether personal or business-related—you should always gravitate towards platforms that offer end-to-end encryption by default. Applications like Signal, ProtonMail, and even secure versions of WhatsApp or Telegram (when set correctly) keep your data private.
- Prevent Data Interception: This isn’t just about preventing eavesdropping; it reduces the chance of attackers intercepting legitimate voice or video data that could be used to train deepfake AI.
- Verify on a Secure Channel: More importantly, when you receive a suspicious request, especially one with a deepfake element, verifying it through a known, secure, and encrypted channel (like a quick voice call using a pre-agreed secure app, or a previously established secure email) can be the difference between falling victim and staying safe. Always remember, if someone is asking for something unusual, a quick, secure verification is your best friend.
5. Browser Privacy: Reducing Your Digital Footprint for Deepfake Protection
Your web browser is your gateway to the internet, and unfortunately, it can also be a major source of data for those looking to create deepfakes or target you with scams. Every website you visit, every cookie you accept, and every social media interaction leaves a digital footprint. Minimizing this footprint is a proactive step in deepfake protection.
Actionable Steps:
- Use Privacy-Focused Browsers: Consider browsers like Brave or Firefox with enhanced tracking protection.
- Install Ad and Tracker Blockers: Add browser extensions that block ads and trackers (e.g., uBlock Origin, Privacy Badger).
- Clear Data Regularly: Regularly clear your browser’s cache and cookies, or set it to do so automatically.
- Be Permission-Aware: Be cautious about the permissions you grant to websites and extensions.
- Starve the AI: By reducing the amount of data collected about you online, you make it harder for deepfake artists to gather the high-quality images, videos, and audio needed to synthesize a convincing fake of you or your team members. Think of it as putting less of yourself out there for AI to learn from.
6. Social Media Safety: Guarding Against Deepfake Exploitation
Social media platforms are treasure troves for deepfake creators. The sheer volume of photos, videos, and audio clips we share publicly provides ample training data for AI. Therefore, how you manage your social media presence is a direct and critical deepfake defense strategy.
How to Spot a Deepfake: Visual & Audio Red Flags to Detect
On social media, you’re constantly exposed to new content, so knowing how to spot a deepfake is vital. While AI is getting better, there are still non-technical red flags to look for:
- Visual Inconsistencies: Pay attention to unnatural blinking patterns, jerky movements, odd lighting or shadows that don’t match the environment, or distorted facial features (eyes, teeth, hands, skin texture often look “off”). Look for flickering edges or blurred backgrounds around the subject.
- Audio Anomalies: Is the voice cadence unnatural? Does the lip-sync seem off? Is there a lack of emotion that doesn’t fit the context? Are there strange pauses or background noise issues that don’t align with the visual?
- Contextual Clues: Be wary of sensational headlines, poor grammar, or spelling in accompanying text. If something seems “too good to be true” or incredibly outrageous, it probably is.
Proactive Steps for Social Media Safety:
- Tighten Privacy Settings: Go through all your social media accounts and tighten your privacy settings immediately. Restrict who can see your photos, videos, and personal information. Make your profiles private where possible.
- Share with Care: Be incredibly cautious about publicly available high-quality media of yourself or your team. Every clear, high-resolution photo or video you share is potential training data for deepfake AI. Minimize what’s accessible to the public.
- Consider Watermarks: If you’re a content creator or small business sharing original media, consider adding watermarks to make it harder for your content to be used for deepfake generation without detection.
- Verify the Source & Trust Your Gut: Always check where content originated, not just where it’s shared. Does the source seem legitimate? Does the story make sense? If something feels off, trust that instinct and pause before reacting or sharing. A simple reverse image or video search can often reveal the history and authenticity of media.
These simple checks and proactive steps can make a significant difference in preventing the spread of deepfake content and protecting your own digital presence.
7. Data Minimization: The Best Defense Against AI-Driven Deception
In the fight against deepfakes, one of your most powerful, proactive strategies is data minimization. Simply put, it means limiting the amount of personal data you share online and keeping your digital footprint as small as possible. This is a core privacy principle that has direct benefits for deepfake protection.
Actionable Steps:
- Review and Reduce: Actively reduce your online footprint by removing old, unnecessary social media posts, declining non-essential data collection on websites, and being mindful of what personal information you make publicly accessible.
- Starve the AI: Why is it so effective? Because AI needs data to learn. The more high-quality images, videos, and audio recordings of you that are publicly available online, the easier it is for malicious actors to train a deepfake model that convincingly mimics your appearance and voice. Less data out there means less raw material for potential deepfakes, making you a much harder target.
- Think Before You Share: Before posting any personal photos, videos, or audio online, consider whether it truly needs to be public. Default to privacy.
8. Secure Backups & Incident Response: Recovering from Deepfake Attacks
Even with the best preventative measures, no one is entirely immune to cyber threats. Deepfake attacks can lead to severe consequences, including financial fraud, data loss, and significant reputational damage. This is why having secure backups and a robust incident response plan isn’t just good practice—it’s essential for recovery.
Actionable Steps:
- Regular, Encrypted Backups: Ensure you’re backing up all critical business data and personal files to an offsite or cloud storage solution. In the event a deepfake-enhanced fraud leads to system compromise or data deletion, you’ll be able to restore your information quickly and efficiently.
- Develop an Incident Response Plan: Know what to do if you encounter a deepfake or, worse, become a victim. This plan should include:
- Report to Platforms: If you see deepfake content on social media or a hosting site, report it immediately to the platform administrators.
- Report to Law Enforcement: If you suspect fraud, harassment, or defamation, contact local law enforcement and relevant cybersecurity authorities.
- Seek Legal Advice: If your reputation or business is significantly harmed, consult with legal professionals immediately.
- Don’t Engage or Share: Avoid amplifying the fake content. Engaging with it, even to debunk, can sometimes spread it further. Your focus should be on removal and containment.
- Communicate Internally (for Businesses): Establish clear internal communication protocols for employees to report suspicious deepfake-enhanced requests without fear of reprisal.
Having a clear protocol for these situations can significantly mitigate the long-term impact of a deepfake attack and ensure a faster, more effective recovery.
9. Threat Modeling: Anticipating the Next Deepfake Frontier
The landscape of AI-powered deepfakes is not static; it’s an ongoing “AI vs. AI” arms race, with creators constantly refining their techniques and detectors working to keep pace. For us, this means that vigilance and continuous learning aren’t just buzzwords—they’re fundamental to our digital safety. Threat modeling, in its simplest form, means thinking about potential threats and how they might impact you or your business, then planning accordingly.
Actionable Steps:
- Stay Informed: Regularly read reputable cybersecurity news and analyses to stay informed about new deepfake tactics and evolving AI capabilities.
- Assess Your Vulnerabilities: Regularly ask critical questions: Could your voice be easily cloned from public videos? Is your company’s verification process robust enough to withstand a deepfake video call? What information is publicly available that could be weaponized against you?
- Adjust Defenses Proactively: Based on your threat modeling, adjust your personal and business defenses accordingly. The future of deepfakes will undoubtedly bring more sophisticated challenges, but by staying proactive and informed, you can be better prepared for whatever comes next.
Empower Yourself: Take Control of Your Digital Security
Protecting your digital life today requires more than just basic cybersecurity; it demands an understanding of sophisticated threats like deepfakes and the practical steps to counteract them. It’s a continuous journey of learning and adaptation, but it’s a journey you can navigate successfully by taking proactive steps.
Don’t wait until you’re a target. Start with the basics: implement a strong password manager and enable 2FA on all your critical accounts today. Then, begin systematically applying the other defense strategies discussed. By empowering yourself with knowledge and implementing these actionable tools, you are not just reacting to threats; you are taking control, building resilience, and safeguarding your digital future against the evolving landscape of AI-driven deception. Your digital security depends on it.